
Sierra Wireless and Sony Semiconductor Israel

Many factors, including new government regulations, increased pressure to generate and deliver utilities in a sustainable way, a need for more accurate billing, and a growing customer demand for better services, are driving utilities to digitally transform their operations.
One of the key aspects of these utilities’ digital transformation efforts has been smart meter deployments. In fact, Mordor Intelligence estimates that smart meter shipments will reach 198.5 million units by 2026, a CAGR of 6.6 % (2021-2026). With smart meters, utilities can collect more detailed and up-to-date data on customers’ electricity, gas, and water consumption, providing them with new and more valuable insights on how to optimize their operations. In addition, smart meters can show more accurate billing for multi-dwelling units such as apartment buildings or other shared spaces.
As they evaluate the next generation of smart meter solutions, lessons learned from previous rollouts, the growing threat of cyberattacks, and the need to future-proof these smart meter solutions are leading utilities to look at several factors such as coverage, data rates and resiliency to ensure a successful deployment.
Two of the most important factors however in helping to ensure a successful deployment are security and the low power requirements.
Security is an ongoing issue with any IoT device, and particularly for smart metering which is part of the critical energy infrastructure. New threats can appear at any time – tomorrow or years from now – so it’s important to be prepared and ready to react. Firmware over-the-air (FOTA) updates make it easier to maintain a robust deployment and ensure transmissions are protected and safe. Whenever new threats appear, FOTA updates let you take immediate action.
However, there are some critical security considerations in a FOTA update system regarding:
One of the first decisions when deciding on an IoT module and FOTA solution for smart metering is where the FOTA platform system is hosted. National regulations on data privacy and security are becoming more and more stringent, and concerns are arising from cyber-criminal organizations. This makes it vital for energy infrastructure providers to be able to identify where the encrypted security keys and FOTA platform is located and who may have access, since access to these two components could enable the hacking of any IoT device.
As a result, more and more designs are using FOTA platforms that are physically located both in Europe and the US, providing the advantage of being locally hosted and controlled, and making sure that encrypted security keys are issued by servers located in these locations.
For devices, an encrypted connection between the device and the server using LwM2M and CoAP protocols -particularly suited for power and data transmission efficiency in cellular connectivity- with DTLS 1.2. should be used to ensure the privacy of data. A pre-shared key should be pre-loaded in the factory, and RSA signatures used for mutual authentication, to retain download integrity and ensure authenticity of the firmware. Also, logins must be restricted by IP address and only accessed with DTLS and mutual authentication keys allowing client devices to verify the identity of the server, and the server to recognize it is a valid IoT device authorized to communicate with.
If a FOTA update is interrupted, due to poor signal strength or a loss of power, the system should be able to automatically resume or restart it. It is vital that if the update fails, the system supports retries, and if the newly installed update doesn’t work properly, a fallback option recovers the previous version. Also, embedded modules can be configured to accept or delay firmware upgrades based on application priorities – so there’s no interruption in device operation – and the modules can monitor their own status during the upgrade, so any problems can be addressed quickly.
Finally, rotating keys on a regular basis helps to meet cryptographic best practices. Automatic key rotation at a defined period, such as every 90 days, increases security and helps to meet security regulations that require periodic, automatic key rotation.
When choosing a cellular module supplier, we recommend utilities review these critical factors as they are part of their entire meter security chain and may impact the economic equation and customer trust should a security breach occur.
When evaluating the power needs for smart meters, most utilities will look at 23dBm and 20dBm options. But what are the advantages and disadvantages of each? Let’s look at the technical requirements, data transfer rates, and the cost analysis to understand.
3GPP defined the LTE 23dBm power class in Release 8, the first release of the LTE standard. This has led mobile network operators to optimize and deploy LTE base stations optimized for 23dBm. These LTE base stations also support Low Power Wide Area (LPWA) LTE-M and NB-IoT networks– the same networks that utilities are increasingly using for smart meter solutions. The impact of this network deployment can be seen in Figure 1 in the Transmission (Tx) Power Cumulative-Distribution-Function (CDF) showing that transmission powers of 23dBm are very commonly used (i.e., often above 50% of the time). The reason for such a distribution is for spectral efficiency optimization. When using maximum power –maximum throughput is achieved for the allocated spectrum resources (frequency and time allocated for the device).
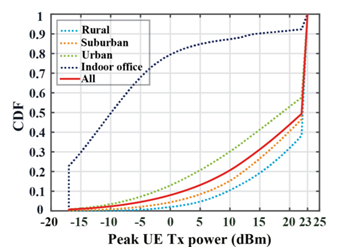
Figure 1: Distribution of Peak UE Transmission power in different scenarios
3GPP then later added a 20dBm power class specification to its cellular telecommunications technology standard. Devices that use 20dBm have lower signal levels at the base station antenna input than 23dBm devices, but the standard lets them make up for this lower signal level with additional repetitions or lower data rates.
dBm is a logarithmic unit. This means that while a decline of 3dBm might seem small, a 20dBm signal is half as strong as a 23dBm signal. This means that 23dBm device transmissions can more easily pass-through obstacles and provide a greater coverage range than 20dBm devices, making it easier for these devices to connect to cellular networks when they are located inside a building, underground, or in rural areas with few cellular towers.
In addition to offering broader coverage than 20dBm devices, 23dBm smart meters also transfer data at a higher rate in challenging coverage scenarios, supporting a wider variety of smart meter applications than 20dBm smart meters. For example, Figure 2 shows that a decline of 3dB in MCL which is similar to 3db drop in transmission power consumption (maximal coupling loss – attenuation between the base station and device antenna) reduces uplink data throughput as much as 50%. This will limit the devices ability to transmit a significant amount of data and will increase the delay of such transmissions.
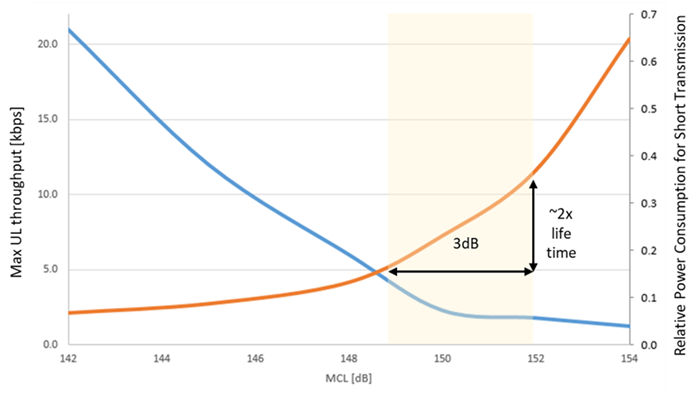
Figure 2: Effect of TX Power difference on device throughput and power consumption
There are other drawbacks beyond weaker coverage and slower data rates associated with 20dBm devices. Though 20dBm devices have lower power, in challenging coverage scenarios 23dBm smart meters consume less power (lengthening their lifetimes) than 20dBm smart meters. This is because lower power 20dBm devices have slower data rates and thus can take twice as much time to transmit their data as 23dBm devices.
Perhaps counter intuitive, however as illustrated in Figure 3 when device transmission power is decreased and compensated with additional transmissions – overall power consumption will increase since the device will be active for longer periods of time.
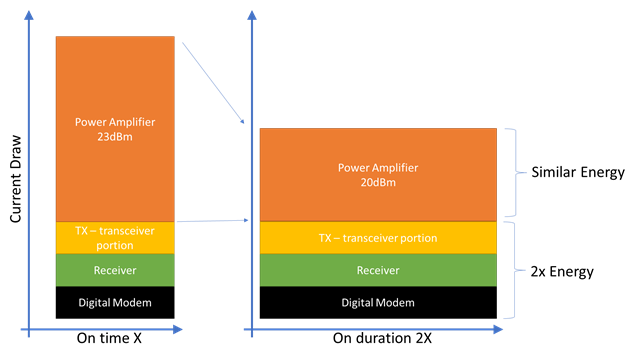
Figure 3: Effect of transmission time on overall power consumption
In simple terms, the power used in a transmission is equal to the (Power Amplifier’s Current + Digital and Analog Circuits Current) * Time of Transmission. Since the 20dBm device will only lower the “Power Amplifier’s Current” and not the other components, when the “Time of Transmission” is increased, the overall power is higher. This leads to the 20dBm device using more power than a 23dBm device for transmissions when they are inside a building, underground, in rural areas or other challenging coverage scenarios, and they end up consuming more from their battery.
As an additional example, Figure 4 illustrates that under certain challenging coverage scenarios a 2dB difference in a smart meter that transmits 10 kilobytes of data a day will increase power consumption of the device by 60% to 70%. For 20dBm versus 23dBm systems, the power difference is even bigger due to the increased time it takes to transmit this data.
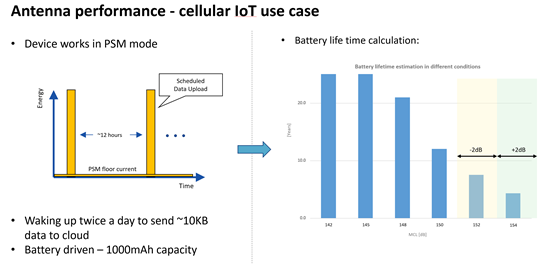
Figure 4: Battery Lifetime versus 2dB coverage difference scenarios
Designing IoT devices to use 20dBm rather than 23dBm can marginally reduce the cost of the devices’ chipsets but, when considering the total cost of ownership, a 20dBm device could be higher.
The overall cost of a cellular module includes digital processing, a radio transceiver, secure element, memories, RX/TX switch, passive elements, PCB, shielding and power amplifier and the cost of manufacturing. In the power amplifier, the cost saving by reducing the transmission power from 23dBm to 20dBm is arguable and depends on the technology and level of integration, however even the most expansive GaAs based power amplifier cost is still a fraction (5-7%) of the overall module cost. Therefore, any cost saving achieved by reducing the transmission power in the PA, is not very significant in the overall cellular module or product cost.
As mentioned above, a 20dBm device is less spectral efficient than a 23dBm device, which means it takes more spectral resources to send a kilobyte (KB) of data. This is very important to MNOs since spectrum is a huge capital investment, so having devices which use more of that very valuable resource ends up costing the MNO more per KB to service. Finally, as mentioned above, the fact that 20dBm devices use more power than 23dBm smart meters in challenging coverage environments means that, for a similar lifespan, these 20dBm need larger (and more expensive) batteries.
Due to the minimal chipset savings, the increase in battery costs, and the potential increase in monthly service costs, the overall total cost of ownership for a 20dBm meter often exceeds that of a 23dBm meter.
Security is a requirement in any industry, but there are additional challenges with implementing smart meters. Utilities should consider key features such as FOTA system updates, (including platform and device), and key rotation to help ensure optimal security of their devices.
For power, smart meters that transmit data using signals with 23dBm (200mW) of power generally have a leg up on smart meters that transmit data using lower power 20dBm (100mW) signals. Given these advantages, and the minimal smart meter chipset and device cost savings associated with using 20dBm smart meter solutions, 23dBm smart meter solutions can better address utilities’ smart meter needs.
For utilities that want to accelerate their digital transformation, understanding the security and power requirements of smart meters can be the key to making this transition successful.
Get innovation delivered to your inbox. Sign up for our blog and stay on top of the very latest from Semtech (formerly Sierra Wireless).